Introduction:
Biometric authentication, particularly fingerprint scanning, is becoming increasingly popular for enhancing security in web applications. The ability to verify users based on their unique fingerprints offers robust protection against unauthorized access. In this blog, we'll walk you through the process of integrating fingerprint scanners with web applications.
Integrating Fingerprint Scanners with Web Applications
Integrating fingerprint scanners with web applications is the process of incorporating fingerprint authentication technology into web-based software or platforms. This integration enhances security and user experience by allowing users to access web applications and perform various actions by simply scanning their fingerprints. Below, we'll delve deeper into this process:
Understanding Fingerprint Scanners:
Fingerprint scanners are biometric devices that capture and analyze the unique patterns of ridges and furrows on an individual's fingertip.
These patterns are converted into digital templates, which are used for identification and verification.
Why Integrate Fingerprint Scanners with Web Applications?
- Enhanced Security: Fingerprint authentication is highly secure as it relies on unique physical attributes.
- Convenience: Users can access web applications without the need to remember passwords or PINs.
- Speed and Efficiency: Authentication is quick, reducing login times and enhancing the user experience.
- Versatility: Fingerprint scanners can be used in a wide range of applications, from online banking to employee attendance systems.
Integration Steps:
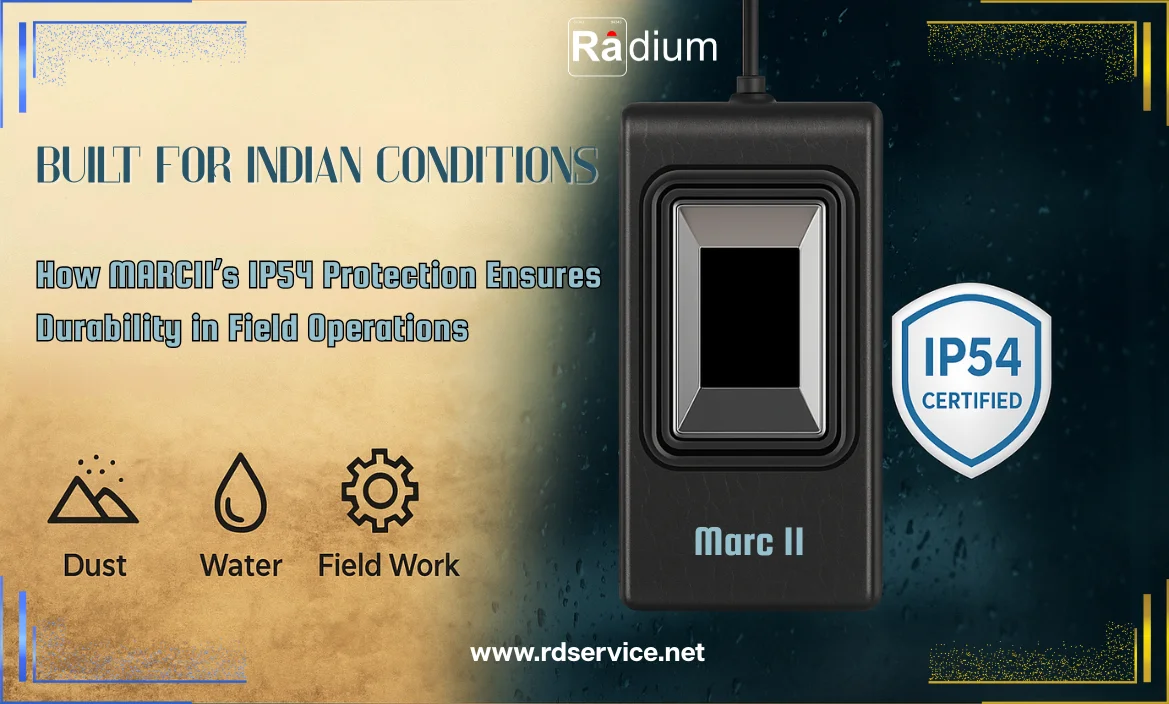
Choosing the Right Fingerprint Scanner:
Select a fingerprint scanner that suits your application's requirements in terms of technology, connectivity, and form factor.
Biometric SDKs and APIs:
Acquire the necessary software development kits (SDKs) and application programming interfaces (APIs) to interact with the fingerprint scanner.
Building Fingerprint Authentication Workflows:
Design authentication workflows that incorporate fingerprint scanning, including user registration, enrollment, and verification processes.
Security Considerations:
Implement robust security measures to protect fingerprint data, such as encryption and secure storage.
Utilize spoofing and liveness detection to prevent fraudulent fingerprint submissions.
The majority of vendors of biometric devices provide APIs (Application Programming Interfaces) so that programmers can connect their unique apps with biometric scanners. With the use of APIs, developers may access and incorporate hardware or services into their solution without having to start from scratch. For example, SecuGen Web API, Aware’s Next Fingerprint, etc.
These exclusive APIs are typically created for a certain product line that the manufacturer offers, so they are incompatible with products under other brands. The user agent (in the case of a web application, the browser) and biometric hardware (such as fingerprint, face, iris, and other biometric readers/scanners) can communicate with each other thanks to these APIs, which include specialized code and instructions.
The World Wide Web Consortium (W3C) and the FIDO Alliance announced the achievement of a significant standards milestone in April 2018. It is anticipated that the new WebAuthn standard would result in more reliable yet straightforward web authentication. WebAuthn outlines how online apps can perform user authentication and access and use biometric devices (along with other forms of authentication).
The Fast Identity Online (FIDO) Alliance submitted WebAuthn to the W3C, a public industry group that develops authentication standards. Major companies like Google, Paypal, Mozilla, Microsoft, and Qualcomm support this standard.
Web browsers and associated web platform infrastructure can use the standard web API defined by WebAuthn. Users can utilize new authentication techniques on the web, in their browsers, and on various websites and devices.
With WebAuthn, users can use public key cryptographic-based biometric authenticators like voice, fingerprint, USB token, YubiKey, etc. as alternatives to password-based authentication environments.
Major web browsers like Chrome, Edge, and Firefox will soon be able to login into online accounts using fingerprint scanners, voice authentication, facial recognition, and other biometric technologies without the use of any additional software, according to a separate W3C announcement.
How does Web Authentication Function?
Web authentication is compatible with various industry standards including FIDO 2.0 Client to Authenticator Protocol 2 and Credential Management Level 1. During registration, the authenticator generates a fresh set of public-key credentials. The relying party's challenge can be signed using this new set of public-key credentials. The public portion of these new credentials can be returned to the relying party for storage together with the signed challenge. When necessary, the relying party can later utilize these credentials to confirm a user's identity.
Conclusion:
Integrating fingerprint scanners with web applications can significantly enhance security and user experience. This technology offers a convenient and secure way to authenticate users, reducing the reliance on traditional passwords. However, it's essential to address privacy concerns, comply with regulations, and provide alternative authentication methods for users without fingerprint scanners. With the right hardware, programming, and user interface design, web applications can leverage biometric authentication to stay at the forefront of modern security practices.